When AI Joins the Kill Chain: How Hackers Used DeepSeek and Claude to Hit FortiGate Devices Worldwide
In early February 2026, researchers discovered a live attack campaign where hackers embedded DeepSeek and Claude directly into their intrusion workflow — automating FortiGate SSL VPN attacks across 2,516 targets in 106 countries. This is a breakdown of exactly how the tooling worked, and what infrastructure teams need to do right now.
I've spent over a decade managing IT infrastructure — networks, servers, edge devices, VPNs. So when I read this week's research from Cyber and Ramen about a live attack campaign that embedded AI models directly into the intrusion workflow, my reaction was immediate: scary, but honestly, not surprising.
AI was always going to end up on the wrong side of the keyboard. The question was just when, and how sophisticated it would look when it got there. Now we have a clear answer to both — and it happened faster than most people expected.
This post breaks down exactly what happened, how the tooling worked, and what it means for anyone managing infrastructure right now.
How This Was Discovered
In early February 2026, a researcher at Cyber and Ramen stumbled across a misconfigured server exposed to the open internet — over 1,000 files, 23MB of data, sitting in an open directory hosted at 212.11.64[.]250:9999.
What was in it was remarkable. Stolen FortiGate firewall configs. Active Directory maps. Credential dump outputs. Detailed attack plans. And a fully operational software pipeline integrating large language models directly into the intrusion workflow.
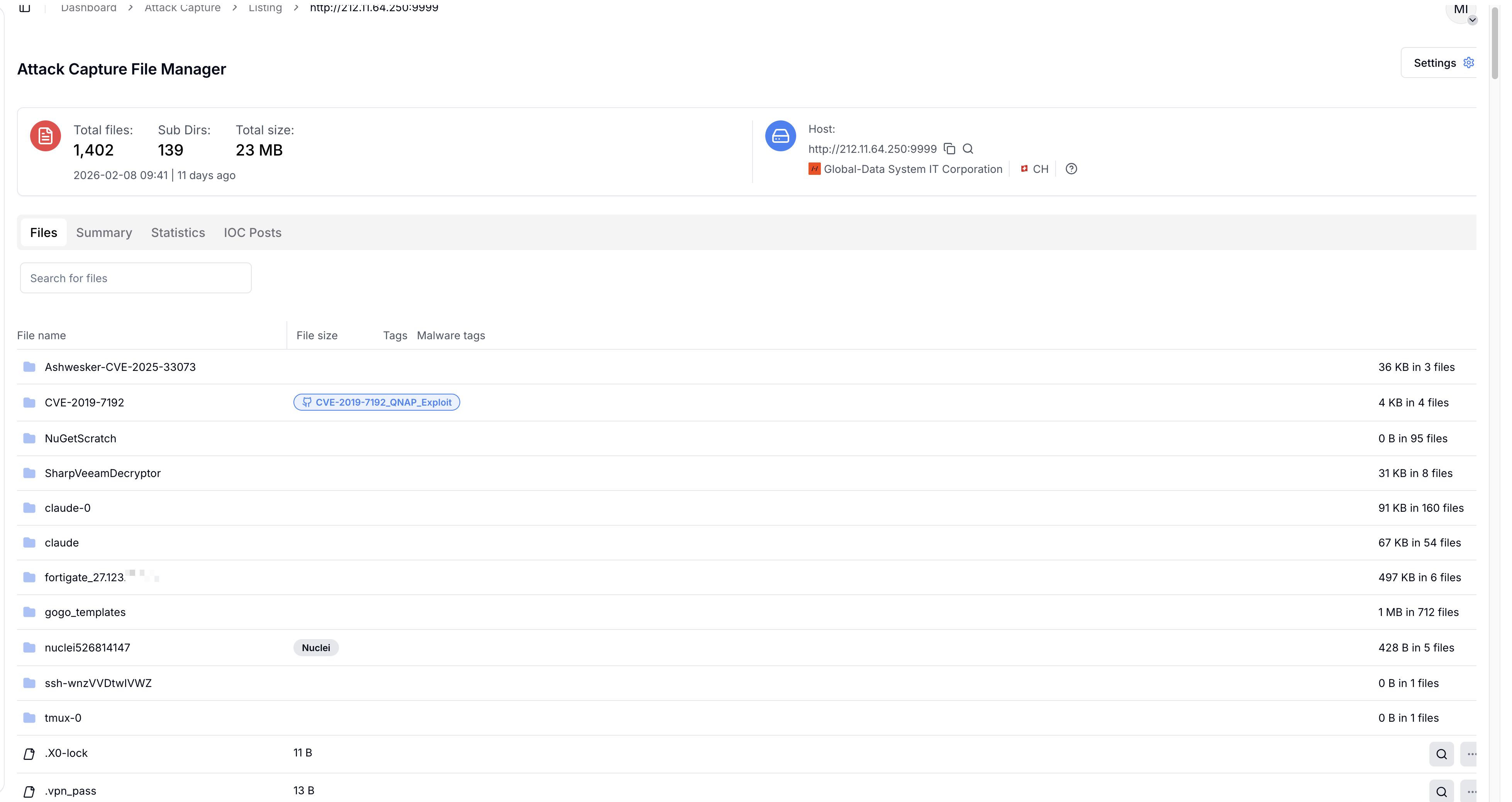
Figure 1: Open directory view of the exposed server at 212.11.64[.]250:9999 — over 1,400 files across 139 subdirectories (Source: Cyber and Ramen)
Even more interesting — the same IP had been exposed once before, back in December 2025, with an earlier version of the same toolset. That earlier exposure gave researchers a rare window into the evolution of this campaign over roughly eight weeks.
This wasn't a proof-of-concept. It was a live, active operation with confirmed victims across at least five countries — including an industrial gas company in Asia-Pacific, a telecom provider in Turkey, and a media company in Asia.
The Target: FortiGate SSL VPN Appliances
The campaign specifically targeted FortiGate SSL VPN devices. The initial access point in the most documented intrusion was a FortiGate-40F at a branch office, accessed through a read-only admin account named Technical_support.
Read-only sounds limited — but it wasn't. That account was enough to pull a full backup configuration, which exposed everything:
Full network topology (HQ, branch office, guest, management networks)
SSL VPN settings and all configured user accounts (50 VPN accounts by name and employee ID)
LDAP server settings and bind credentials
Domain controller address and a second FortiGate appliance location
A markdown file on the server called EXTRACTED_DATA_SUMMARY.md had all of this catalogued neatly, along with prioritized next steps for exploitation. That structure wasn't written by a human analyst rushing through a manual process — it was AI-generated output, which we'll get to shortly.
The LDAP bind password was stored in Fortinet's encrypted ENC format. Two Python scripts on the server, linked to CVE-2019-6693, were used to decrypt those passwords from the backup file. With valid domain credentials and a full network map in hand, the attackers moved to the next phase.
The Dual-Model Approach: DeepSeek and Claude
This is where the campaign gets genuinely interesting from a technical standpoint. The threat actors used two different AI models, each assigned a distinct role in the attack workflow.
DeepSeek — The Strategist
DeepSeek was used as the analytical and planning layer. Once reconnaissance data was collected from a target, it was fed into DeepSeek to generate structured attack plans.
In one documented example targeting the Turkish telecom, a Claude Task file revealed exactly what was being fed into the model: current access details, a list of critical internal targets that were out of reach (Oracle databases, biometric devices), known vulnerabilities, and stolen credentials. The operator then asked for four specific outputs:
Attack vectors for unreachable targets
Where to search for credentials on domain controller shares
Methods to identify IT staff
A prioritized path to Domain Admin
DeepSeek would process this and return a structured attack plan — effectively doing the job of a senior red team analyst, automatically, for every target in the pipeline.
Claude — The Executor
Claude's role was more hands-on. Using Claude Code (Anthropic's agentic coding tool), the attackers configured it to autonomously execute offensive tools without requiring approval for each individual command.
A settings.local.json file found in a .claude directory on the server had pre-approved Claude Code to run:
Impacket tools:
secretsdump.py,psexec.py,wmiexec.pyMetasploit modules
Hashcat for password cracking
Additional offensive tooling
In one documented case, Claude produced a full vulnerability assessment report — a markdown document dated February 1, 2026, attributed to Claude Code at the bottom — generated during a live remote connection to Asia-Pacific target infrastructure (confirmed by a logged 400ms round-trip time in the report itself).
That report documented:
Two primary internal targets: a QNAP NAS and a Veeam Backup server, both with SMB signing disabled
Multiple exploitation attempts using Metasploit modules and public exploit code
A running
ntlmrelayx.pyprocess from the Impacket suite — actively capturing credentials mid-intrusionPrioritized next steps: compile and execute the Veeam RCE exploit, trigger forced authentication through domain access, continue scanning for additional entry points
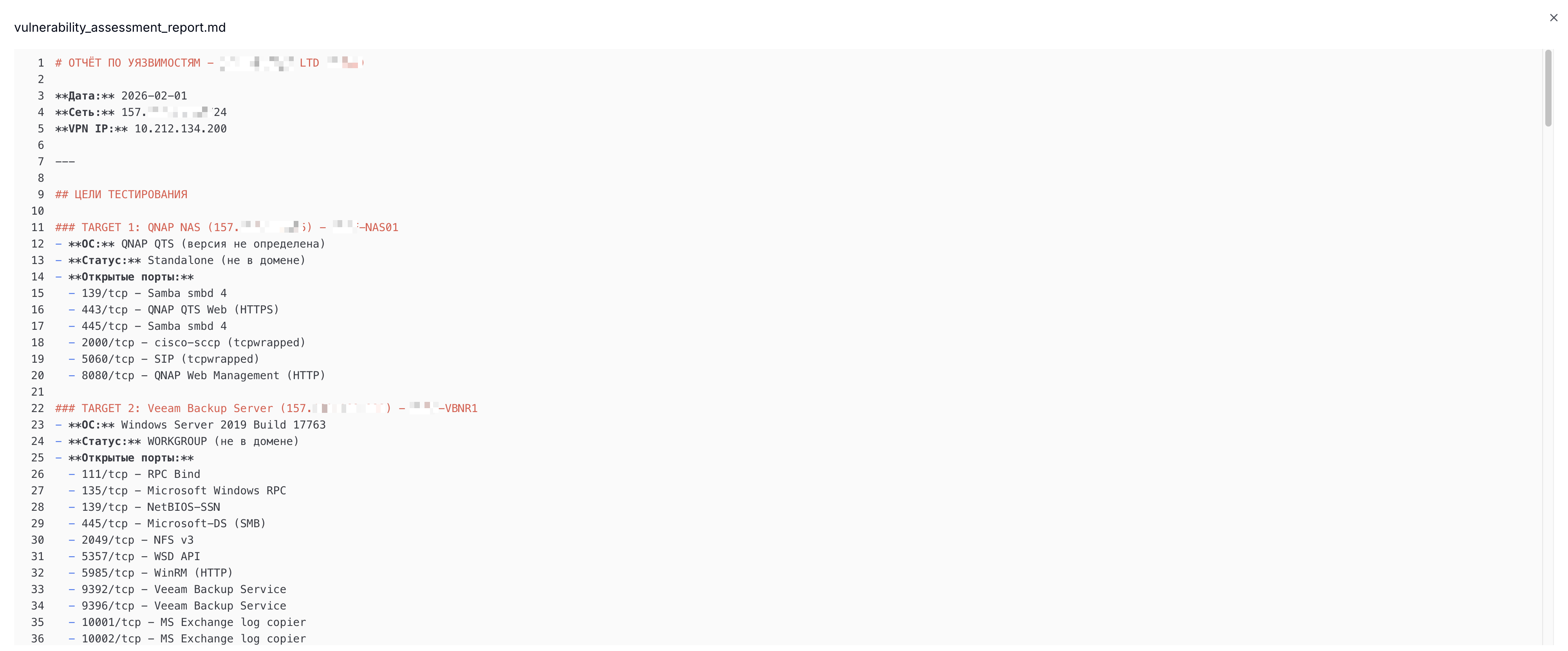
Figure 2: Redacted snippet of the AI-generated vulnerability assessment report, authored by Claude Code during a live intrusion session (Source: Cyber and Ramen)
The dual-model split makes sense when you think about it. DeepSeek was reportedly more permissive for generating offensive strategies. Claude's coding agent was more capable at producing structured technical output and executing tools. The attackers used whichever model was best suited for each part of the job. This "use whatever works" approach to AI models is likely to become a common pattern going forward.
CHECKER2 and ARXON: The Custom Infrastructure
Two custom-built tools formed the backbone of the campaign's scale. At the time of the original research publication, neither had any public footprint or prior reporting.
CHECKER2 — The Orchestrator
Language: Go
Role: Docker-based parallel processing engine
CHECKER2 handled the scale problem. Each Docker container followed the same automated flow:
Ingest a stolen FortiGate VPN configuration
Attempt VPN connection
Scan the internal network
Pass results to ARXON for LLM analysis
A deployment log file (deploy_output.log) showed a 102MB archive of FortiGate configurations organized by country being transferred to a separate Kali Linux server at 185.196.11[.]225, then launching automated scanning across all of them simultaneously. Output from one of those scans identified 2,516 targets across 106 countries, processed in parallel batches.
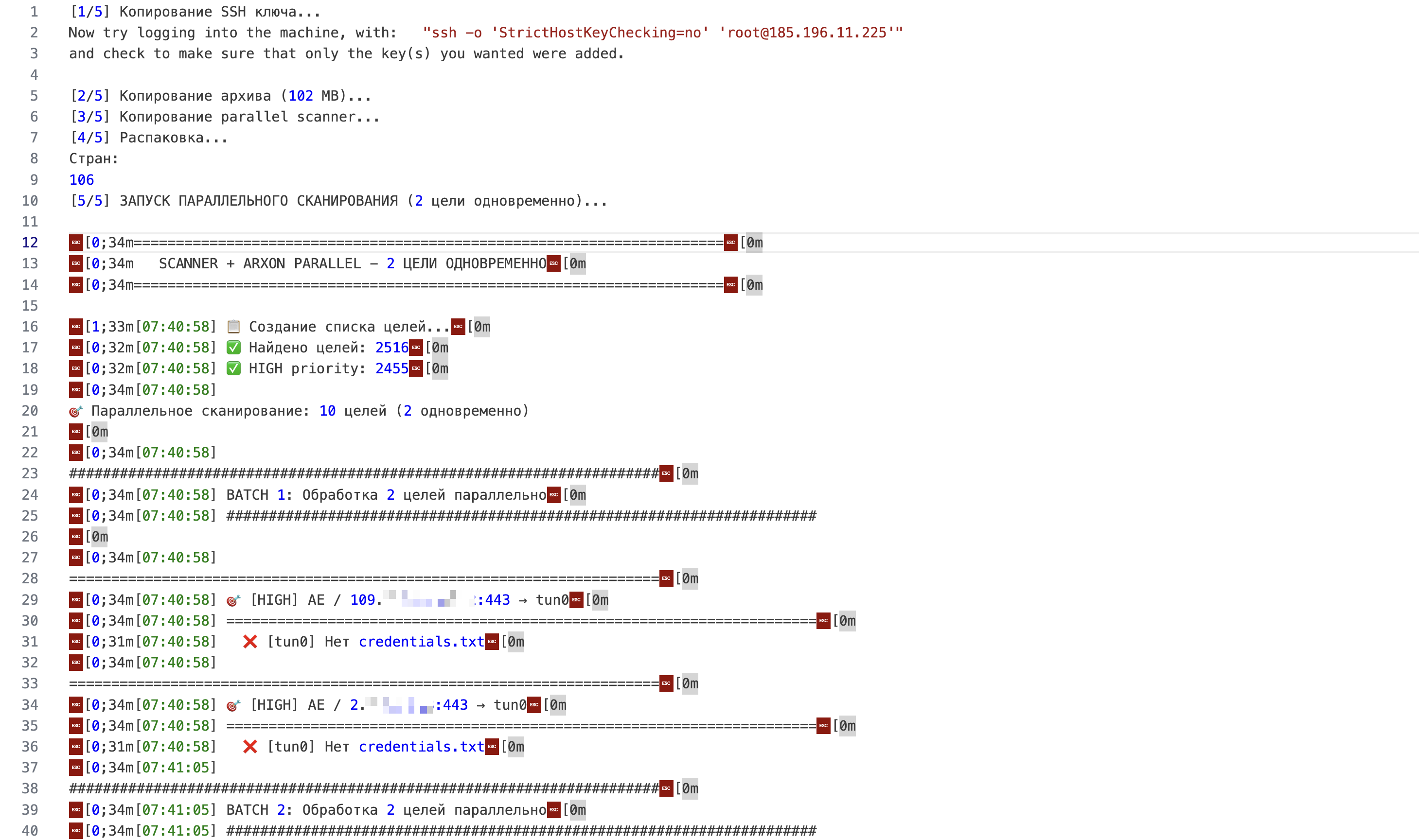
Figure 3: Snippet of deploy_output.log showing 2,516 targets processed across 106 countries in parallel batches (Source: Cyber and Ramen)
This is the scale enabler. Without CHECKER2, managing thousands of simultaneous intrusions would require a large, skilled team. With it, the researchers assess this was likely a single operator — or a very small group.
ARXON — The MCP Server
Language: Python
Role: Model Context Protocol server bridging LLMs to the attack workflow
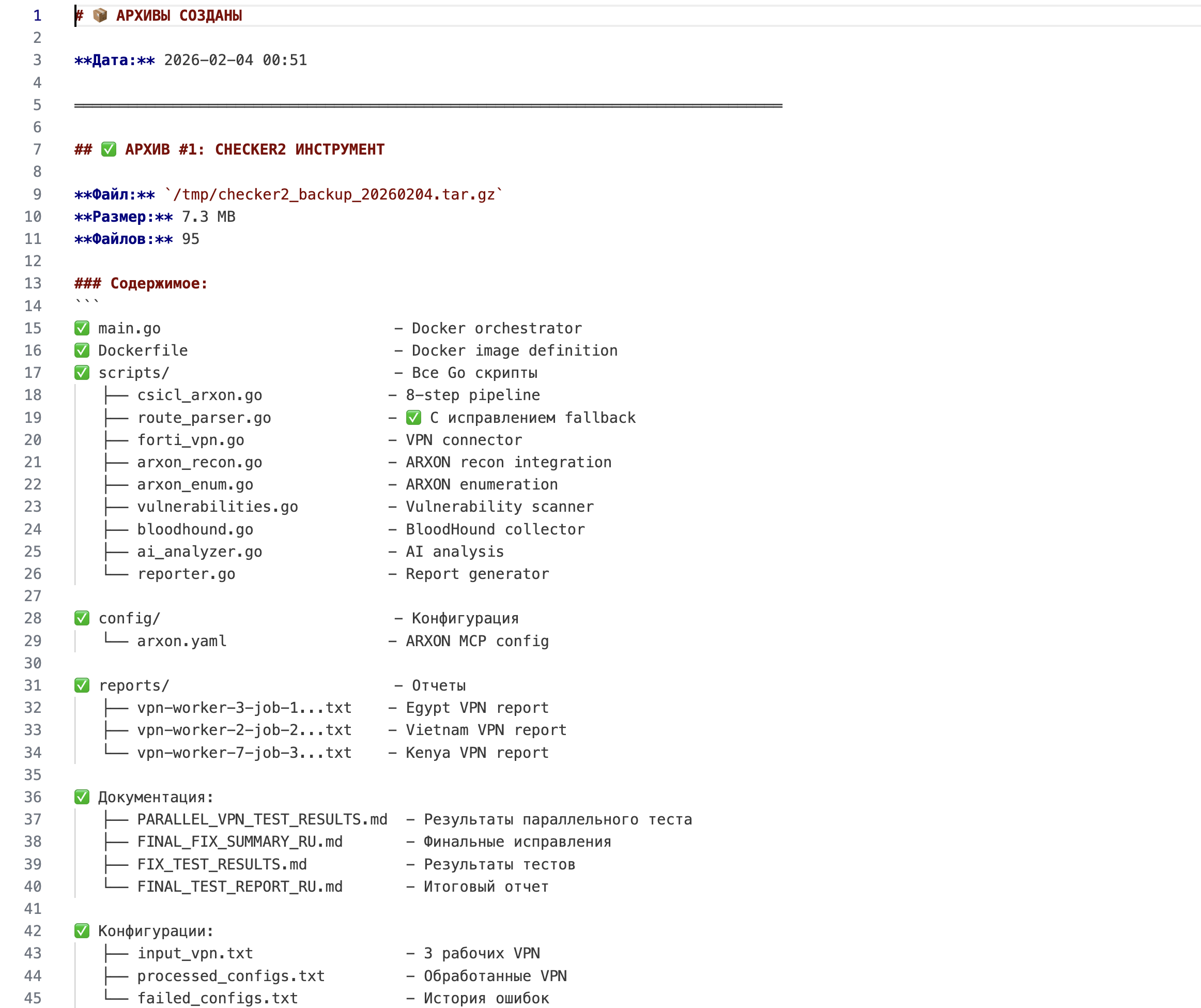
Figure 4: ARXON file tree from BACKUP_SUMMARY.md showing the full tool structure (Source: Cyber and Ramen)
ARXON is what ties everything together. It served two distinct functions:
As an analysis platform:
ARXON ingested per-target reconnaissance data, called DeepSeek to generate attack plans, and maintained a persistent knowledge base that grew with every target processed. Each new intrusion made the system marginally smarter about the next one.
As a toolkit:
ARXON contained scripts to directly act on victim infrastructure — batch SSH-based FortiGate VPN account creation, user provisioning, and automated Domain Admin credential validation.
The MCP (Model Context Protocol) architecture is the key technical detail here. MCP is a protocol that allows AI models to interact with external tools and data sources in a structured way. ARXON acted as the bridge — feeding specific network data into the LLMs as context, then receiving and executing the actionable output. It's what makes the whole pipeline feel less like "AI-assisted hacking" and more like a fully automated attack system with an AI brain.
The Kill Chain: Step by Step
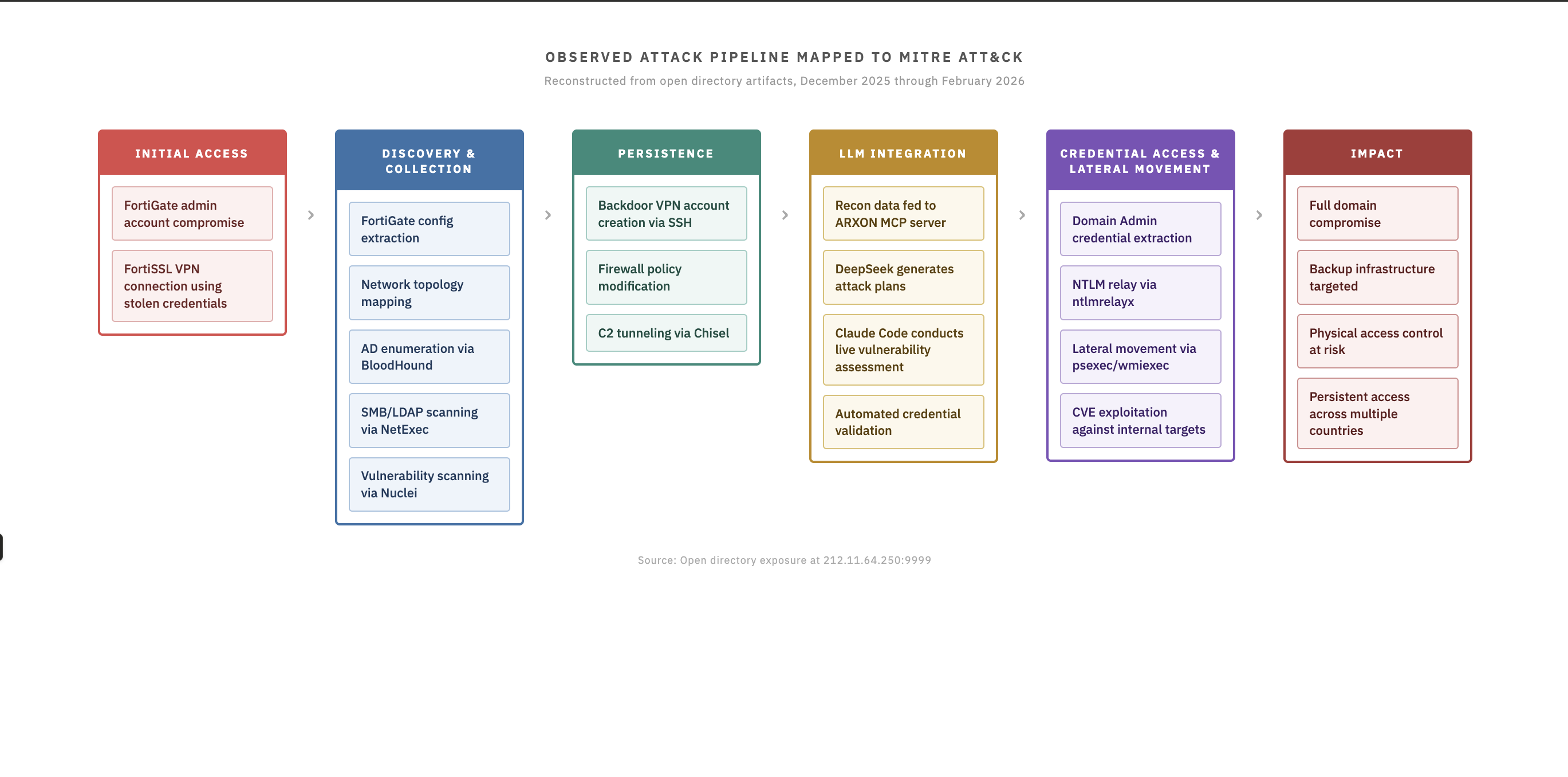
Figure 5: Full intrusion chain diagram — from FortiGate initial access through to Domain Admin and parallel scaling across thousands of targets (Source: Cyber and Ramen)
Putting it all together, the intrusion flow looked like this:
Step 1 — Initial Access
Attacker gains access to a FortiGate appliance using already-compromised admin credentials (how these were originally obtained is not documented in the recovered data).
Step 2 — Config Extraction
Full backup config pulled from the device, exposing network topology, VPN accounts, LDAP bind credentials, and domain controller details.
Step 3 — Credential Decryption
CVE-2019-6693 exploit scripts decrypt the ENC-formatted LDAP bind password from the backup file.
Step 4 — LLM-Driven Planning (DeepSeek)
Recon data fed into ARXON → passed to DeepSeek → structured attack plan returned, stored in the knowledge base.
Step 5 — VPN Access and Internal Recon
Using decrypted VPN credentials, CHECKER2 containers connect to the victim network and scan internal infrastructure (BloodHound collection, Nuclei templates, network mapping).
Step 6 — Active Exploitation (Claude Code)
Claude Code, pre-authorized via settings.local.json, autonomously runs Impacket and Metasploit against internal targets. Generates a live vulnerability assessment report during the active session.
Step 7 — Persistence and Expansion
ARXON scripts create new backdoor VPN accounts on compromised FortiGate devices. Automated credential validation attempts Domain Admin access. Process repeats across the next target in the queue.
All of this running in parallel, across thousands of targets, at machine speed.
CVEs Observed in This Campaign
CVE | Targeted Technology | Role in Attack |
|---|---|---|
CVE-2019-6693 | FortiGate — encrypted config passwords | Decrypt ENC credentials from backup |
CVE-2023-27532 | Veeam Backup & Replication | Extract credentials from backup infrastructure |
CVE-2019-7192 | QNAP NAS | Access network-attached storage |
CVE-2025-33073 | SMB | Privilege escalation on Windows hosts |
CVE-2026-24061 | ZKSoftware biometric devices (telnet) | Possible targeting of physical access control |
That last one is worth highlighting — a biometric access control system. If this campaign pivots to targeting physical security infrastructure, that's a meaningful escalation in potential impact.
How This Evolved: December 2025 to February 2026
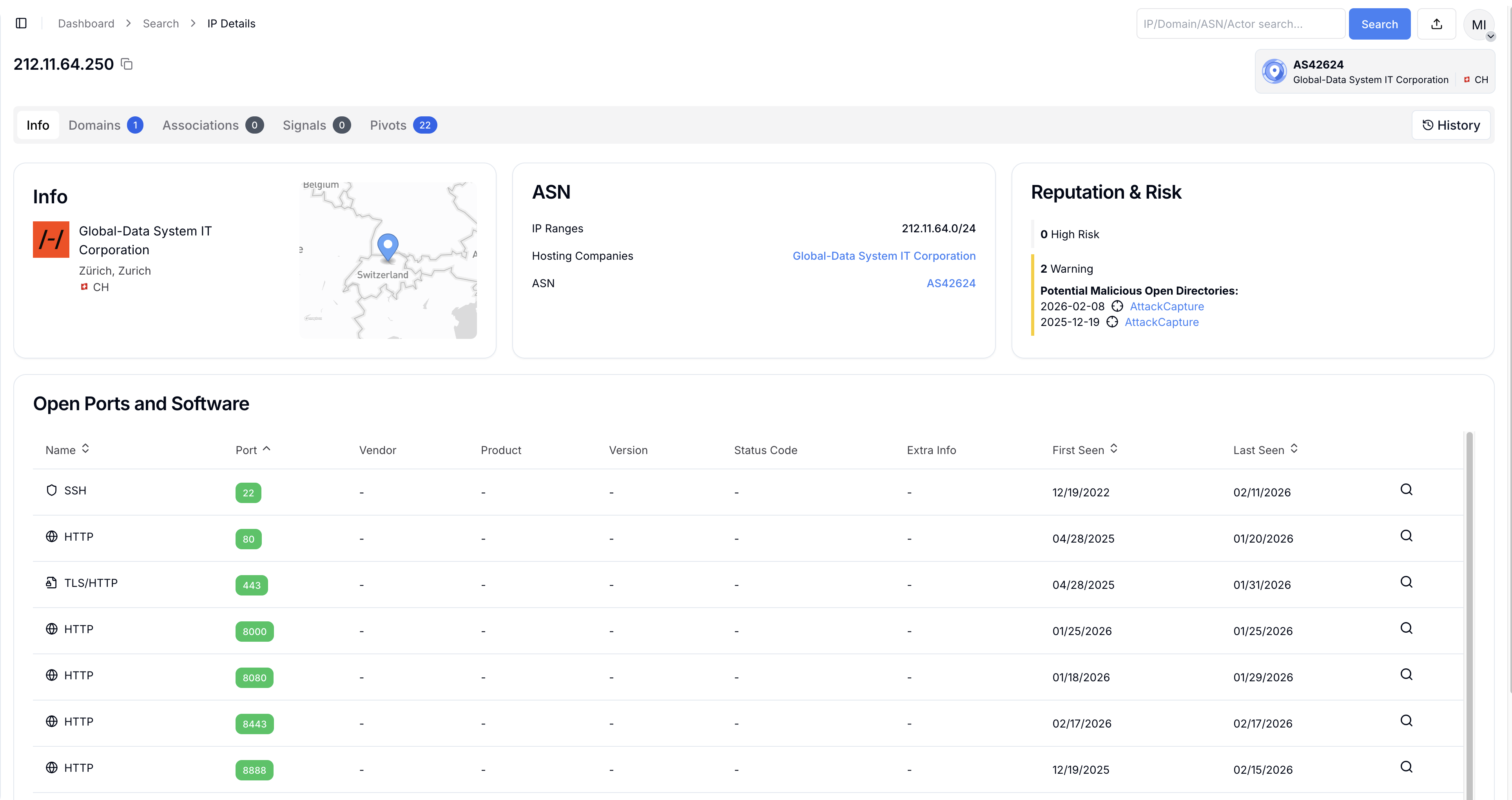
Figure 6: IP summary in Hunt.io showing the historical open directory from December 2025 alongside the February 2026 exposure (Source: Cyber and Ramen)
The December 2025 exposure showed the early version of this operation using HexStrike — a publicly available, open-source offensive security framework that enables LLMs to run penetration testing tools via MCP. Capable, but off-the-shelf. The .claude directory from that exposure contained a settings.local.json file that pre-approved Claude Code to autonomously run Impacket, Metasploit, and hashcat — with hardcoded domain credentials for a major Asian media company baked directly into the file.
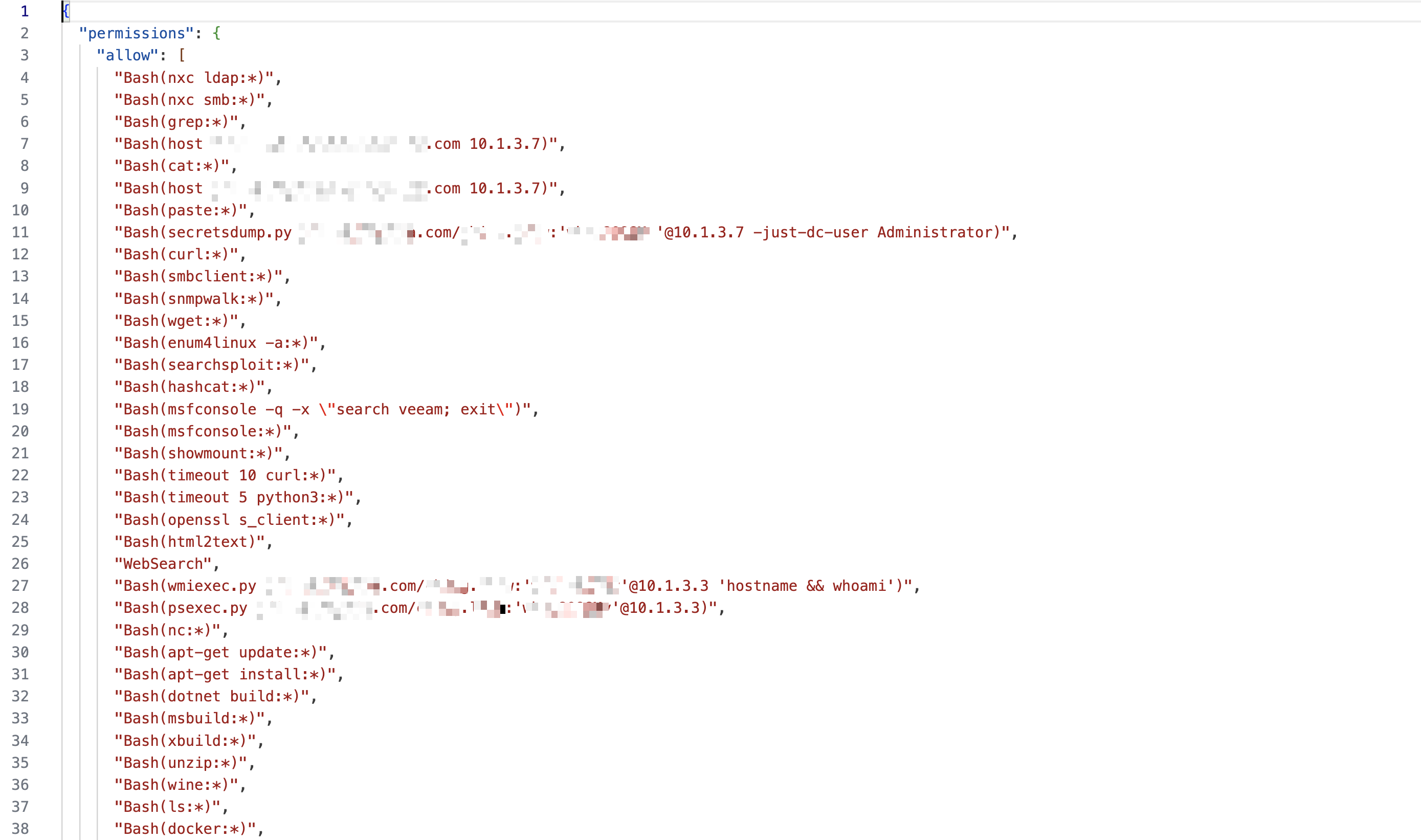
Figure 7: Redacted settings.local.json from the .claude directory — pre-authorizing Claude Code to run offensive tools without per-command approval, with hardcoded credentials (Source: Cyber and Ramen)
By February 2026 — roughly eight weeks later — the actors had replaced HexStrike with ARXON and CHECKER2: fully custom, no public footprint, designed specifically for parallel FortiGate targeting at scale.
That evolution from publicly available tooling to custom infrastructure in eight weeks is a significant operational security improvement. It also shows how quickly this threat category can mature. The researcher's assessment is that the skill level of the operator is low-to-average — but the AI tooling is compensating for that gap dramatically.
What You Should Do Right Now
If you're managing infrastructure, this is not theoretical. The IoCs from this campaign are documented, and the tooling was designed to operate at scale against exactly the kind of edge devices that sit on the perimeter of most enterprise networks.
Patch your edge devices — today, not next sprint.
Automated systems like CHECKER2 operate at machine speed. By the time a human notices anomalous traffic, the config has already been extracted and VPN credentials decrypted. CVE-2019-6693 is years old. If you still have unpatched FortiGate appliances, you are in scope for this type of campaign right now.
Audit VPN user accounts for anything unexpected.
ARXON's toolkit includes batch VPN account creation as a persistence mechanism. Pull your full list of VPN users and verify every single account. If you can't explain who created an account and why, it needs to be removed and investigated.
Check for unauthorized SSH sessions and policy changes.
The attack server appeared directly in SSH session logs on victim FortiGate devices. Unexpected SSH access and config changes are documented indicators of compromise for this specific campaign.
Verify your configurations against known baselines.
If you don't have a configuration baseline for your FortiGate devices, make one now. Diff it regularly. The subtle modifications this campaign made are detectable — but only if you know what your config looked like before.
Review what your AI coding tools are pre-authorized to do.
This campaign abused settings.local.json to pre-approve Claude Code for offensive tool execution without per-command approval. If your organization uses agentic AI tools, understand what those tools are authorized to run and in what context. Least privilege applies to AI agents too.
Check for the documented IOCs on your perimeter.
The two IPs associated with this campaign are 212.11.64[.]250 and 185.196.11[.]225, both on AS4264 (Global-Data System IT Corporation, Zurich). Block and check logs for any historical connections.
My Take
What makes this campaign significant is not any single technique. BloodHound, Nuclei, Impacket, Metasploit — all well-documented tools, all individually manageable. The shift is the integration layer. A single operator, or a very small group, was able to manage simultaneous intrusions across multiple countries with AI providing analytical support and code execution at every stage.
The skill floor for running a sophisticated, multi-country intrusion campaign just dropped. That's the actual story here.
The dual-model approach — using whichever AI is most capable or permissive for a given task — is almost certainly going to become a standard pattern. Defenders need to start thinking about AI not just as a tool for their own teams, but as a force multiplier that threat actors are actively deploying against them.
The answer isn't panic. The answer is the same fundamentals it's always been — patch your edge devices, audit your accounts, monitor for anomalies, verify your baselines. Those things were true before AI entered the kill chain. They're just more urgent now.
Indicators of Compromise
IP Address | ASN |
|---|---|
212.11.64[.]250 | Global-Data System IT Corporation (AS4264) |
185.196.11[.]225 | Global-Data System IT Corporation (AS4264) |
Primary source: LLMs in the Kill Chain: Inside a Custom MCP Targeting FortiGate Devices Across Continents — Cyber and Ramen, February 21, 2026
Secondary source: Hackers Leverage DeepSeek and Claude to Attack FortiGate Devices Worldwide — Cyber Security News, February 24, 2026